How FortiSOAR Works: Practical Use Cases for Modern Security Operations
Dive into how FortiSOAR helps your organization to better coordinate its alerts and response.
Dive into how FortiSOAR helps your organization to better coordinate its alerts and response.
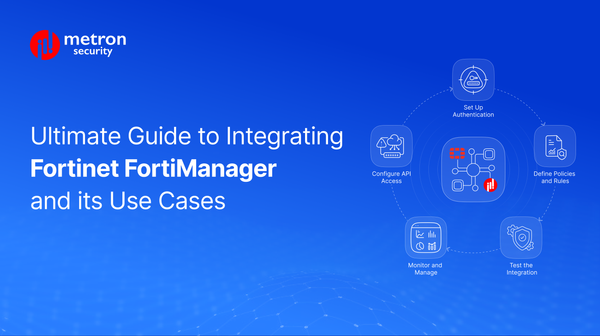
Get a handle on the process of integrating Fortinet Fortimanager, along with several of its key use cases

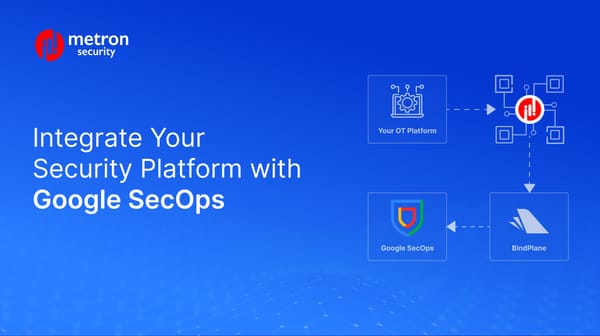
How to integrate Google SecOps with third-party platforms like Digital Risk Protection.

Divine into the FortiGate Architecture from packet flow to real-world use cases

Discover how Breach and Attack Simulation platforms can continuously test your security environment.

Discover why Identity Threat Detection and Response (ITDR) is rapidly gaining traction alongside traditional IAM.

Dive into some of the top use cases that organizations can hope to get out of a next-gen SIEM like Falcon Logscale.

Discover 5 real-world AWS Security Hub and CSPM integrations.

Discover how Microsoft Sentinel integrations improve unify your security operations at scale.

Discover how CrowdStrike Falcon integration helps stop complex attacks across hybrid and cloud environments.
Learn how to integrate CI alerts into Google SecOps SIEM to boost IoT/OT visibility.
Dive into five real-world use cases for integration Google SecOps with EDR.

A well-integrated and seamless security ecosystem is no longer simply optional.

Discover how your team can make the best use of the NVD-CVE Fetcher-APP for Splunk.

Discover JupiterOne’s vital features, benefits, and integration capabilities among others.

Discover how Metron's expertise in BAS integrations can help you achieve a seamless and successful integration with SafeBreach.