Connecting Your SIEM to AWS: Tips and Considerations (2024)
In the following post, we discuss tips and considerations for connecting your SIEM with AWS for efficient cloud security and optimization.
Alexander Nachaj
As your organization, service offerings, and data grow, effectively managing the cloud aspects of your security can become increasingly challenging. Notable pain points include gaps in visibility that become even more pronounced as you enter each stage of growing pains, along with the possibility for vulnerabilities and breaches to go undetected. Without centralized tools and integrations keeping your apps connected, these problems may rapidly become exacerbated.
To work around these issues, organizations are increasingly turning to SIEMs (Security Information and Event Management systems) to act as the command center of their security operations.
In the following post, we discuss strategies and considerations for connecting your SIEM with AWS (Amazon Web Services) for efficient cloud security and optimization.
Before Connecting Your SIEM to AWS
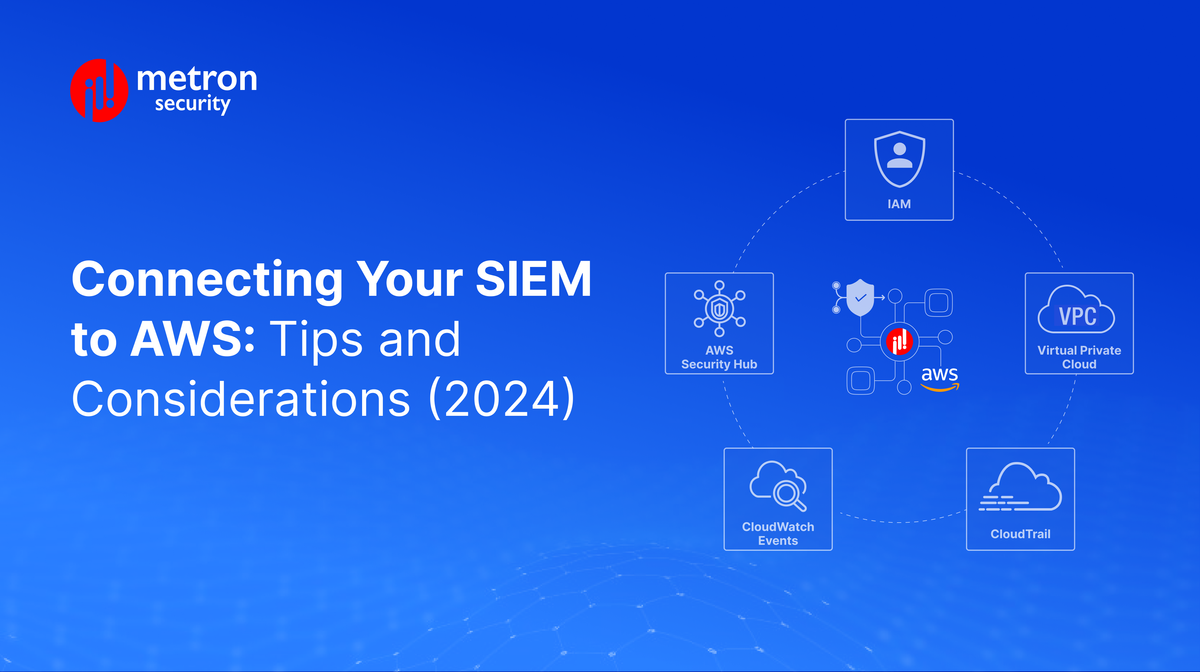
Connecting your SIEM to AWS involves working with various components and services of both platforms, including but not limited to:
- Data ingest services
- Data transfer methods
- Response mechanisms within your SIEM
Before beginning, and to better ensure a seamless integration between the two platforms, it is important to understand what is available through your SIEM but also to consider the service options provided by AWS. Most SIEMs offer comprehensive documentation on their websites or on-call support. If either are not available, be sure to connect with a trusted integration partner.
Key AWS Data Sources and Services
AWS is a versatile platform, offering plenty of options for integration from the various sub services available. Depending on your specific integration requirements, you may need to collect data into your SIEM from each service individually. In the lists below, we outline some of the key services and sources you may need to work with during your integration process.
One prominent AWS data source is Identity and Access Management (IAM). This is a robust service that facilitates the assignment of permissions and credentials based on users, groups, or roles. IAM can play a pivotal role in managing credentials, specifying access, and federating credentials with on-prem systems. Access to IAM data is available through logs stored in S3, AWS Security Hub, or API calls.
The next service to consider would be the Virtual Private Cloud (VPC) Flow Logs. This tool offers a granular view of security groups and access control list (ACL) events. This data is instrumental in identifying system misuse, analyzing rejection rates, correlating traffic flow changes, and verifying server or port access. Access to VPC Flow Logs data is handled through CloudWatch Logs or the designated S3 bucket log storage.
Another important data source for integration purposes is CloudTrail. This service enables continuous monitoring and logging of account activity across various AWS interfaces, including the Management Console, SDKs, other AWS services, and command-line tools. CloudTrail also collects information from security, audit, VPC flow logs, and API calls, delivering data to S3 every five minutes. Access to this data can occur either directly from S3 logs or through CloudWatch Logs and CloudFormation.
CloudWatch Events acts as a service that automates response actions triggered by specific events. This capability extends to other services such as Lambda or Simple Notification Service (SNS), allowing for the creation of response workflows initiated automatically in response to trigger events, effectively sending data to your SIEM.
AWS Security Hub is a service for centralizing alerts and findings from multiple services like GuardDuty, Macie, IAM Access Analyzer, and AWS Firewall Manager. This centralized hub allows continuous monitoring and automated compliance checks within your environment.
Conclusions
As is the case with all cloud-first environments, continuous response and data integrity are key to managing your security and minimizing risk. When connected with AWS or other cloud services, a well integrated SIEM at the heart of your security operations can enable your team to efficiently monitor and respond to incidents and issues from across your repertoire of services and tools.
Metron is a trusted provider of on-demand and effective approaches to managing third-party integrations for security ecosystems. With extensive experience in delivering automation solutions for over 200 security applications, Metron has earned the trust of numerous fast-growing security companies and managed security service providers (MSSPs).
Metron’s transparent development processes, deep understanding of security products, and fixed-cost model have resulted in shorter development times and significant cost savings for clients compared to deploying internal engineering teams for similar tasks. You can connect with Metron at connect@metronlabs.com.